What happened?
Recently, some security holes in Exchange servers have been closed, but the scams continue.
Heise.de reports about a fraud attempt in which previously stolen e-mail communication was used to initiate a payment by the recipient via a typo-squatting domain in which, for example, numbers are substituted for letters (he1se.de).
An existing email communication was used to send a known email history with new payment information to the fraud victim via this new domain. Additional recipients known to the victim were also added to increase credibility.
Securityexpert Sophos recommends hardening the relevant email servers:
Next, defenders can make it easier for other organizations to determine the legitimacy of emails coming from their domain, for instance by implementing industry recognized standards for email authentication, such as SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain Message Authentication Reporting and Conformance.) Using these standards can make it harder for an attacker to send spoofed emails impersonating your domain.
So what to do now?
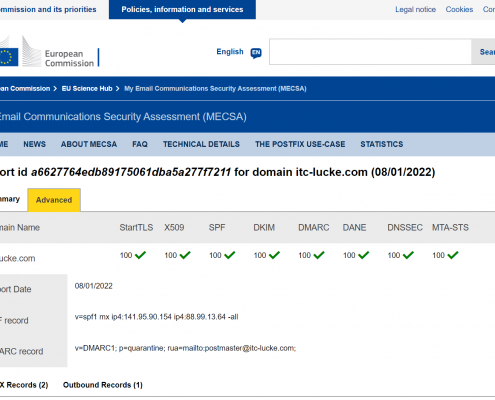
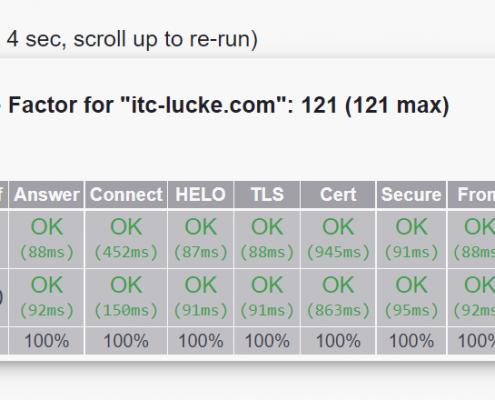
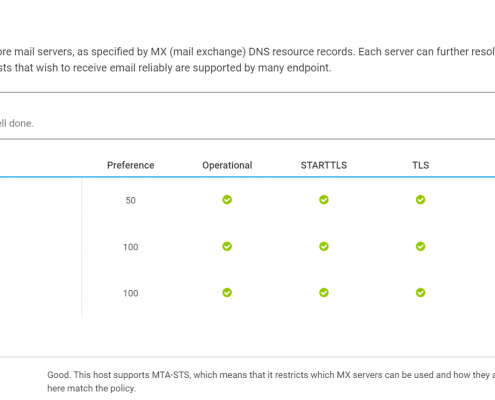
As Sophos recommends, your email servers should have the most common and up-to-date security features. SPF, DKIM and DMARC are essential, but we also add DNSSEC, MTA-STS/DANE to the servers and disable older and insecure encryption in communications.
If you want to check your email servers, feel free to drop by our Service section of Hardening. We will be happy to advise you on security issues regarding your own email servers and help you meet the maximum security standards.
Conclusion:
Using our own mail servers as an example, we would like to briefly demonstrate how your mail servers could also perform after being secured. A really nice side effect is also that you will receive much less SPAM messages, because SPAMERS usually do not make this effort and therefore your mail server will reject them directly.